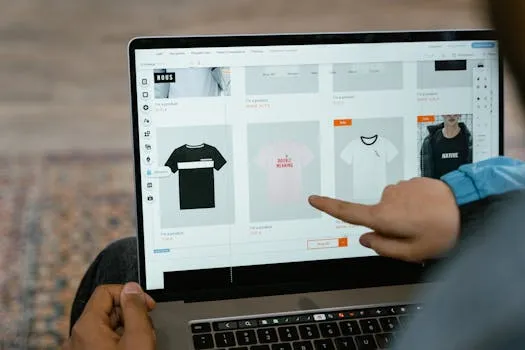
Is your store leaking revenue?
Find out exactly where you're losing sales — takes 2 minutes.
Securing your eCommerce store is one of those tasks that feels optional — until it's too late. Most online store owners in Malaysia and Singapore think they're too small to be a target. Why would anyone hack a store doing RM30,000 a month? We've worked with dozens of eCommerce businesses that asked exactly that question — right before they got hacked. The reality is that most attacks aren't targeted. They're automated scripts that scan the internet for vulnerable websites and exploit them indiscriminately, regardless of how big or small the store is.
According to Sucuri's annual website threat report, over 60% of hacked websites are small-to-medium businesses. And in eCommerce, the stakes are higher than for a regular website — you're handling customer payment data, personal information, and business-critical inventory. A security breach doesn't just take your store offline; it destroys customer trust, triggers potential regulatory issues under Malaysia's Personal Data Protection Act (PDPA), and can cost thousands in cleanup and lost revenue.
What Happens When an eCommerce Store Gets Hacked?
Understanding the real-world consequences makes security feel less abstract:
Quick Answer: How do you protect your ecommerce store from hackers?
Five non-negotiables block 99% of automated attacks: strong unique passwords, two-factor authentication, software updates, SSL certificates, and a web application firewall. Over 60% of hacked websites are small-to-medium businesses, and most attacks are automated scripts — not targeted. These five measures take less than a day to implement.
| Attack Type | What Happens | Business Impact |
|---|---|---|
| Defacement | Your store's content is replaced with the hacker's message | Loss of sales, brand reputation damage |
| Malware injection | Hidden code infects your visitors' devices | Google blacklists your site, traffic drops to zero |
| Credit card skimming | Checkout form secretly sends payment data to attackers | Legal liability, PCI compliance violations, customer lawsuits |
| SEO spam injection | Hidden pages sell counterfeit products on your domain | Google penalises your rankings, months to recover |
| Ransomware | Your store and data are encrypted until you pay | Days of downtime, ransom payment, data loss |
| Botnet recruitment | Your server is used to attack other websites | Hosting provider shuts you down |
The common thread: these aren't sophisticated, targeted attacks. They're mass-automated scripts exploiting known vulnerabilities — outdated software, weak passwords, and unpatched plugins. Cover the basics, and you block the vast majority of threats.

What Is on the Essential Security Checklist?
Tier 1: The Non-Negotiables (Do These Today)
These five practices block roughly 99% of automated attacks. Every eCommerce store — regardless of size — should have these in place:
1. Use strong, unique passwords everywhere
Never reuse passwords across services. Use a password manager like 1Password or Bitwarden to generate and store random 20+ character passwords for every account — your store admin, hosting, email, payment gateways, and domain registrar.
2. Enable two-factor authentication (2FA)
Turn on 2FA for every account that supports it — especially your store admin panel, hosting account, and domain registrar. Even if a password is compromised, 2FA stops the attacker from logging in. Use an authenticator app (Google Authenticator, Authy), not SMS — SMS-based 2FA can be intercepted.
3. Keep all software up to date
Outdated software is the number one entry point for automated attacks. This includes:
- Your eCommerce platform (Shopify handles this automatically; WooCommerce requires manual updates)
- All plugins, themes, and extensions
- Your server's PHP version and operating system
- Any third-party integrations
For WooCommerce stores, see our detailed WooCommerce Security Patching Guide 2026.
4. Install an SSL certificate
SSL encrypts data between your visitors' browsers and your server. Without it, login credentials and payment information are sent in plain text. Most hosting providers include free SSL via Let's Encrypt. Shopify includes SSL automatically on all plans.
5. Use a web application firewall (WAF)
A WAF sits between your store and the internet, blocking malicious traffic before it reaches your server. Options:
| WAF Provider | Best For | Starting Price |
|---|---|---|
| Cloudflare | All stores (free tier available) | Free - $20/month |
| Sucuri | WooCommerce / WordPress stores | $199/year |
| Shopify built-in | Shopify stores | Included in all plans |
For Malaysian stores, Cloudflare has edge servers in Kuala Lumpur and Singapore, meaning your security layer also improves your site speed for local visitors.
Tier 2: Best Practices (Do These This Month)
6. Limit admin access
Only give admin access to people who absolutely need it. Use the principle of least privilege — if someone only needs to manage products, don't give them access to payment settings or code.
7. Set up automated backups
Back up your store daily — database and files. Store backups in a separate location from your server (cloud storage like AWS S3 or Google Cloud). Test restoration quarterly to make sure your backups actually work.
- Shopify: Automated backups via apps like Rewind or BackupMaster
- WooCommerce: Use UpdraftPlus or BlogVault
8. Monitor for suspicious activity
Set up alerts for:
- Failed login attempts (more than 5 in 10 minutes = potential brute force)
- New admin users created
- Changes to payment settings
- Large bulk exports of customer data
9. Secure your payment processing
Never store credit card data on your server. Use payment gateways that handle PCI compliance for you:
- Malaysia: iPay88, Billplz, Revenue Monster, Stripe (now available in Malaysia)
- Singapore: Stripe, PayPal, Atome, GrabPay
- Shopify: Shopify Payments handles PCI compliance automatically
10. Implement Content Security Policy (CSP) headers
CSP headers tell browsers which scripts are allowed to run on your pages. This prevents cross-site scripting (XSS) attacks — one of the OWASP Top 10 vulnerabilities — from injecting malicious code into your store. Building customer trust goes beyond technical security — visible trust signals like reviews, badges, and testimonials also play a critical role. See our guide on 10 social proof strategies for Shopify stores for the full playbook.
Which Is More Secure: Shopify or WooCommerce?
The platform you choose significantly impacts your security workload:
| Security Aspect | Shopify | WooCommerce |
|---|---|---|
| Hosting security | Managed by Shopify (enterprise-grade) | Your responsibility |
| SSL certificate | Included automatically | You set up (usually free via hosting) |
| Software updates | Automatic, no action needed | Manual — you update WordPress, WooCommerce, plugins |
| PCI compliance | Level 1 PCI DSS compliant (highest level) | You must ensure compliance yourself |
| WAF / DDoS protection | Built-in | You add Cloudflare or Sucuri |
| Backup & recovery | Shopify handles infrastructure backups | You configure and manage backups |
| Plugin security | App store review process | Open ecosystem, higher risk from poorly coded plugins |
| Cost of security | Included in subscription | $200-500/year for WAF + backup tools |
Our recommendation: For store owners who don't have a dedicated technical team, Shopify's built-in security is a significant advantage. For WooCommerce stores, partner with a managed hosting provider that handles server-level security, and install a WAF like Cloudflare or Sucuri.

What Should You Do If Your Store Gets Hacked?
If the worst happens, act fast:
- Take the store offline immediately — Put up a maintenance page to prevent further damage to visitors
- Change ALL passwords — Store admin, hosting, database, FTP, domain registrar, payment gateways
- Scan for malware — Use Sucuri SiteCheck (free) or your WAF's malware scanner
- Restore from a clean backup — Go back to the most recent backup before the breach
- Identify the entry point — Check server logs to understand how the attacker got in
- Patch the vulnerability — Update the software, plugin, or configuration that was exploited
- Notify affected customers — If customer data was compromised, Malaysian PDPA requires notification. Be transparent.
- Strengthen defences — Implement any missing items from the checklist above
Bottom Line
Securing your eCommerce store isn't complex — it's just easy to neglect until something goes wrong. The five non-negotiables (strong passwords, 2FA, software updates, SSL, and a WAF) block 99% of automated attacks and take less than a day to implement. Add automated backups, admin access controls, and payment security best practices, and your store is protected against the vast majority of threats. Don't wait for a breach to take security seriously — the cost of prevention is a fraction of the cost of recovery.
Not sure where your store stands? Get a free ecommerce scorecard — we'll audit your store and show you exactly what to fix first.
Frequently Asked Questions
How much does eCommerce security cost?
On Shopify, security is included in your subscription — SSL, PCI compliance, WAF, and hosting security are all built in. On WooCommerce, budget RM800-2,000/year for a WAF (Cloudflare Pro or Sucuri), backup solution (UpdraftPlus or BlogVault), and security monitoring. Either way, the cost is trivial compared to a breach.
What should I do if my store gets hacked?
Take your store offline immediately, change all passwords, scan for malware, and restore from a clean backup. Then identify the entry point (check server logs), patch the vulnerability, and notify affected customers. If customer payment data was compromised, consult legal counsel regarding PDPA notification requirements.
Is Shopify more secure than WooCommerce?
Shopify handles hosting security, PCI compliance, SSL, and platform updates for you — making it inherently more secure for store owners without a dedicated technical team. WooCommerce is equally secure when properly maintained, but that maintenance (updates, backups, WAF, monitoring) is your responsibility. Most security breaches on WooCommerce stores come from outdated plugins.
Keep reading:

Free Download
We audited 10 Shopify stores doing $1M–$20M. Here are the 15 leaks every one had.
Real screenshots (names blurred). Most operators have 8 of the 15 and don't know it.
From 10 audits across SG, MY, AE — fashion, beauty, electronics, food.
PDF in your inbox in 30 seconds. 1 email. No follow-up unless you ask.